Contents: Introduction * Summarization * Substitution * Transposition * Tools and Examples
It may seem a little silly to include a section on cryptography (the science of creating and revealing secret messages) in an encyclopedia of textual criticism, and the author can hardly deny that cryptography is not a main concern of textual critics -- or even of serious Biblical scholars (as opposed to the sort who go about trying to "solve the mystery" of the Apocalypse when the only genuine mystery is why people keep thinking they can "solve" it). But it's worth noting that the well-known Biblical scholar Ronald Knox was actually a cryptologist, working with Britain's famous "Room 40" to solve German ciphers during World War I; in addition, one of the men who cracked the vital Zimmerman Telegram was William Montgomery, who edited an edition of Augustine's Confessions. Others involved in British cryptography at this time include the papyrologist A. S. Hunt and the paleographer Ellis H. Minns. Ward M. Manly, one of the leading lights of the American MI-8 intelligence service in World War I (responsible among other things for the instruction of new cryptographers) did not work on classical or biblical literature, but he did co-edit the Manly-Rickert edition of The Canterbury Tales, the leading critical edition for many years. There seems little question that the same skills that make good textual critics also make good cryptographers. (I will admit that both interest me, though I am no cryptographer and my place in textual criticism is at best debatable.)
And it's worth remembering that we do
find encryptions of sorts in the Bible: Jeremiah 25:26, for example,
has an encrypted name, and presumably the "Number of the
Beast" in Revelation 13:18 represents some sort of cryptogram.
It's just possible that there are others -- if we knew where to
look.
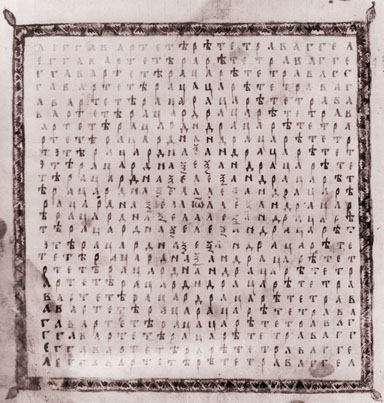
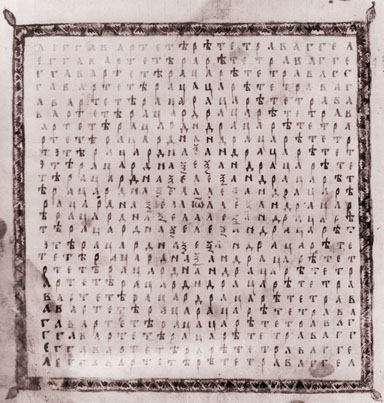
And there are instances of cryptograms of sorts in the marginalia of Biblical manuscripts. I seem to recall hearing of a few instances where scribes' names appeared to be hidden in code. And there is a famous Slavonic gopels, the Gospels of (Bulgarian) Tsar Ivan Alexander, British Library Additional MS. 39627 (dated 1356) which contains a "magic square" (in effect, a transposition code) with information about the manuscript's history. In the case of Tsar Ivan's gospels, that information is hardly needed, since there is full information elsewhere in the manuscript. But if the true colophon had been lost, the ability to read the Magic Square could have been vital. (A reduced black and white scan of this Magic Square is shown at right. A larger image, with an extensive description of the manuscript though no text, can be found in the British Library's volume The Gospels of Tsar Ivan Alexander.)
We find encrypted passages in other manuscript-era works as well, such as an astronomical treatise from the era of Chaucer. It's even thought that some Egyptian hieroglyphs are encrypted messages. It seems certain that we have encoded Babylonian astrological tablets -- tablet British Library 92685, for instance, is a table of some sort, with six columns of numbers (coordinates?) and then what appears to be an explanation. Since we have only part of the tablet, and it is encoded, not one has ever figured out this particular scheme.
Let's start with a few terms. First, encryption is the process of taking some sort of message and concealing it by turning the meaningful message (the "plaintext") into something that, at first glance, looks meaningless (the "ciphertext"). Decryption is the process of taking the ciphertext and converting it back to the original plaintext. There are two sorts of decryption -- what we might call "hostile" and "friendly." Friendly decryption occurs if you are the intended recipient and have been told what you have to do to convert the message. The method used to convert it is known as "the key." A key usually consists of two parts: A method and a specific piece of data used to apply the key -- usually, in cryptography, a set of letters and numbers used to conceal the message. Think of a combination lock: To open it, you must know how all combination locks work (right to the first digit, left to the second, right to the third) and the combination (23-16-21, or whatever). Because cryptographic methods are fairly standard, it is common to refer to the "combination" alone as the "key," rather than applying that term both to method and specific data.
Hostile decryption (now usually technically known as "cryptanalysis") occurs if you intercept the message and manage to decrypt it even though the key has not been voluntarily revealed to you. Typically this entails deducing the key, by logic or by trial and error.
There are, in general, two ways to encrypt a message: By code and by cipher. Codes consist of substituting one set of words for another -- e.g. one might say "Throw out the garbage tomorrow morning" to mean "attack at dawn" or "Tomorrow's menu includes sausage" for "buy pork bellies." A famous real-world example is the Japanese government's signal "East wind, rain" to announce war with the United States in 1941. We also see codes, of a primitive sort, in the Bible, e.g. at Rev. 14:8, 16:19, 17:5, 18:2, 10, 21, where "Babylon" is used as a substitute for Rome. The problem with codes is their inflexibility -- if you don't have a code symbol for "enemy on our flank," and the enemy is on your flank, you have no way to encrypt this vital message. Serious codes are generally nearly unbreakable without some sort of key (unless you have large numbers of messages, anyway, and at least an idea of what some of them are about) -- but they are limited in their usefulness. And if they are compromised (by the capture or theft of a codebook), they are gone forever.
Hence the cipher. Ciphers, instead of replacing words and phrases by other words and phrases, replace letter by letter (or, these days, in blocks of letters) Since there are only a finite number of letters (26 in the Roman alphabet, plus whatever other symbols you wish to include such as spaces and numbers and punctuation), you can make up a rule to cover all possible messages. And, if your first version is compromised, you can just change the key and you are once again safe, at least temporarily.
Concealed messages have an ancient and venerable lineage, and though messages in the past were most often concealed steganographically (i.e. they were physically hidden, written in invisible ink or hidden inside other objects), true cryptography was also occasionally used. Ciphers have been known since ancient times, though the earliest ciphers were almost pathetically simply compared to modern encryption schemes. We won't worry about such modern devices as the Enigma machine or public key cryptography, which (while fascinating) truly have no part in textual criticism. But classical scholars do care about ancient ciphers.
And that means textual critics must care. The reason is that encrypted information is easy to damage. That usually matters relatively little if you know the key to the cipher, and the cipher is a simple one-to-one replacement; you can decrypt the message, fix the errors, and then correct the encrypted form. But if you don't know the key, and have to decrypt the message, think how complicated it is to decrypt it! Even if you have the correct key, you may get nonsense.
Let's give an example of this point, using a simple cipher known since ancient times: The "Caesar cipher." Julius Caesar, to encrypt his messages, used a simple substitution, usually a three-letter offset (i.e. A became D, B became E, C became F, and so on to X, which became A, etc.). So the text "THIS IS A CIPHER" would become "WKLV LU D FLSKHU." (This cipher technique is described, e.g., in Suetonius, Julius LVI. Augustus LXXXVIII tells of the variant used by that monarch: A single-letter shift, A becoming B, B becoming C, etc., up to X becoming AA; if Suetonius is right, this is less secure, because the fact that A would occur only rarely, and always twice, is a clue to the form of the cipher.)
OK, now assume that, instead of an encrypted passage one sentence long, you have many paragraphs in cipher text. Or, rather, assume you're a scribe confronted with this. What are the odds that all that nonsense will be copied correctly?
And now assume that you come along much later and have to decrypt
this damaged message and have to figure out what it says. There are
tools available for decrypting ciphers -- indeed, the author is not
aware of any unsolved ancient cryptographic methods. But the easy
methods of decrypting all assume an intact original, making it easy
to recognize the code. That, in fact, appears to be why we can't
solve the Babylonian cipher cited above: We don't have the first part
of the ciphertext to give us some idea of what we're looking at!
We may illustrate this easily by looking at the "Caesar
cipher" above. Suppose that, instead of
WKLV LU D FLSKHU,
the scribe had copied it as
WRLV LU D FLSKHU
(changing the second letter -- a
change that could easily happen in some Roman writing styles).
You come along and say, "Hm. Looks like a
Caesar cipher." So you start working back, and find that the
first word decrypts as TOIS. If you believe the message to be in
English, this makes nonsense, so you conclude, incorrectly, that it is
not a Caesar cipher.
The good news is that modern cryptographic methods, which are very susceptible to damage and which are unusually difficult to crack, are just that: modern. They require advanced machinery (these days, usually computers, but the German Enigma machine was mechanical and required mass-produced encoder/decoder cams).
Basically, ancient ciphers followed one of three methods: substitution, transposition, and summarization.
Summarization (my own term) is perhaps best dealt with first, since it's actually a class of methods, and it's also formally uncrackable (you can never know you have the right answer). This is because it destroys information. A summarized message gives no clue to its meaning; it's just some sequence which equates to the value of the message. For example, we already mentioned Revelation 13:18 and the "number of the beast." This is actually what a computer person would call a checksum: Take the numerical values of the letters, add them up, and record the result.
We can do this for English messages -- e.g. assign the value A=1, B=2, C=3... Z=26. If we take our "THIS IS A CIPHER" text, for instance, it has the following checksum:
T H I S = 20 + 8 + 9 + 19 = 56
I S = 9 + 19 = 28
A = 1 = 1
C I P H E R = 3 + 9 + 16 + 8 + 5 + 18 = 59
TOTAL = 144
Unfortunately, this information is completely un-decryptable. Suppose you know that a message has "value" 144. The number of possible such messages is very large. It could represent "This is a cipher." It could also represent 144 instances of the letter A. Or six instances of the letter X. Or twelve instances of the letter L. Only a computer could list all the possibilities, and the number of possible readings gets larger and larger as the number gets larger. With a checksum of 144, we know that the number of letters is at least six and no more than 144. Now imagine a checksum of, say, 40,000. That's a minimum message length of 1539 letters, a maximum of 40,000, and a likely value of about 3400 letters. (In a long sample, you can estimate that the total number of letters is about equal to the total divided by 11.7; that's the "average value" of a letter in English, which tends to use the letters early in the alphabet more often than those late in the alphabet.) I doubt even a computer could grind out all the possible values for a checksum of 40,000 in a reasonable time.
And even if you somehow knew the values, it doesn't do you any good, because you don't know their order. Take our message "THIS IS A CIPHER." The letters in this message are ACEHHIIIPRSST. We can arrange these in all sorts of ways. For instance, for all we could tell, it might stand for
IS THIS A CIPHER
or
THIS A CIPHER IS
or, if we are deliberately trying to confuse potential spies,
IS THA CIPHER, IS
(mis-spelling words and adding waste syllables is a recognized method of making deciphering harder).
It could also stand for
ACE HIRST IS HIP
(meaning perhaps that it is safe to talk to Ace Hirst).
And there are doubtless other possibilities I could find if I used a computer rather than my head.
Which brings us to our second method of summmarization, the anagram. ACEHHIIIPRSST, for instance, is an anagram of THIS IS A CIPHER. Same letters, different order.
This is a well-known method of publishing hidden messages.
Christiaan Huygens, for instance, announced his discovery of
the ring(s) of Saturn with an anagram -- a long message which
only he could unscramble:
AAAAAAACCCCCDEEEEEGHIUIIIIIILLLLMMNNNNNNNNNOOOOPPQRRSTTTTTUUUUU
which rearranges to spell
Annulo cingitur tenui plano, nusquam cohaerente, ad ecliptican inclinato
allowing him to claim credit without
looking stupid if he turned out to be wrong.
(On the other hand, Huygens was clearly a coward or he would have
stood up and announced rather than using a trick to claim
credit from someone else who had the courage to say what he saw!).
Galileo had earlier done something similar, telling Kepler of the
phases of Venus with the anagram
Haec immatura a me jam frustra leguntur OY
which rearrances as
Cynthiae figuras aemulatour mater amorum
This may sound
like it wouldn't work very well as a method of assuring meaning
or secrecy, but
it does. Taking a long string of letters and rearranging it to mean
something is tricky; note that Galileo's rearrangement left him
with two leftover letters (OY) which he had to stick on the end.
Thus an anagram is a safe way to assure priority.
A third, partial, form of summarization may just possibly be used in the Old Testament. It's easier to explain in English. The method consists of mashing the whole alphabet into half. So if we line up all 26 letters of the English alphabet with 13 in the first row and 13 in the second, as follows,
| A | B | C | D | E | F | G | H | I | J | K | L | M |
| N | O | P | Q | R | S | T | U | V | W | X | Y | Z |
we then set both A and N equal to A (or, theoretically, to N), both B and O equal to B, etc. Under this method, e.g., THIS IS A CIPHER becomes GHIF IF A CICHEE.
Theoretically, if one used an alphabet with a different number of letters, one could have other such "mashing" methods. A 24-letter alphabet allows unusually many possibilities -- you can line up the first twelve letters with the second twelve, or have three lines of eight letters (e.g. alpha, the first letter; iota, the ninth, and rho, the seventeenth, would all be reduced to alpha), or even four rows of six letters each. The latter form certainly would offer a great deal of security....
The possible instance of the Hebrew form of this, known as "albam," occurs in Isaiah 7:6, which refers to the invading powers setting up the "son of Tabeel" to rule Judah. Tabeel is unknown. The proposal of the Midrash Rabbah on Numbers 18:21 is that "Tabeel" (TBL) is an albam of "Remaliah" (RML), obviously without the last syllable. As with most summarization ciphers, this is possible -- but only possible, and the Midrash gives no reason to actually think it happened. Historical chronicles are full of instances of names we simply can no longer identify.
If a summarization encryption is textually damaged, there really is no recourse. Take that case of Revelation 13:18. We're quite confident that the number of the beast is 666. But we have a variant of 616. Suppose that variant had been more popular, or that some other variant (say 566) had been widely known. Without knowing the thing summarized, and with no basis for decision based on external evidence, how can we ever solve the cipher? We think it refers to Nero -- and yet, this really doesn't make much sense; the emperor Domitian is a much more likely target. So are we sure we know what 666 means? No.
Fortunately, we have more hope when dealing with substitution ciphers. These retain redundancy, so it is sometimes possible to eliminate errors.
A substitution cipher is one in which one letter is substituted for another. The "Caesar cipher" is a substitution cipher: A became D, etc. Caesar is also said to have sent messages in Latin but written in Greek letters (i.e. "THIS IS A CIPHER." would become "QIS IS A SIFER)."
Modern substitution ciphers have become very elaborate, using all sorts of tricks to fool potential decoders. For example, we see the use of nulls. Instead of just using 26 letters, an encoder might throw in a half dozen other symbols at random (so instead of an alphabet of ABCDEFGHIJKLMNOPQRSTUVWXYZ, you might use ABCDEFGHIJKLMNOPQRSTUVWXYZ#$%&!@, with #$%&!@ being merely symbols you throw in at random; they have no meaning. Alternately, you can use extra characters as multiple expressions for the same letter. E.g., since E is the most common letter in English, you could let either # or ! stand for E, so that neither # nor ! is the most common symbol). Another trick is continuously varying the ciphering algorithm. For example, you could apply a continuous Caesar cipher: In the first letter of the message, offset by one letter (so A becomes B, etc.). For the second letter, offset by two (A becomes C, etc.). For the third, offset by three. And so forth. All of these methods are designed to fool deciphers who work based on the table of frequencies of letters.
None of which was needed in ancient times. In the Biblical era, as best we can tell, no one knew which letters were most frequently used. So a simple substitution (one letter always replaces by the same letter -- a so-called mono-alphabetic substitution) was fairly secure. (Before you say, "Well, just try some combinations," remember that the number of such ciphers is huge. There are only 26 Caesar ciphers, but 26 factorial possible substitution ciphers. That's 403,291,461,129,999,980,156,682,240 possible monoalphabetic substitutions for the 26-letter Latin alphabet. For the Greek alphabet, it's 620,448,401,730,000,065,134,592 possibilities (more if we include the three numbers not used as letters). You can't hope to crack that by trial and error without a crib.
It is said that Arabic scholars studying the Quran were the first to learn the rules for decrypting simple substitution ciphers. (One suspects that Hebrew scholars, with their detailed attention to the individual letters of the MT, also had the data they needed. But they probably weren't sending too many secret messages in Hebrew; the language itself, by then, was a pretty good secret medium!) In any case, the substitution code used in the Bible (the above-cited case of Jeremiah 25:26, etc.) is very simple: it's called atbash, because it involved reversing the alphabet. Aleph became taw; bet became shin, etc. An equivalent for the Latin alphabet would be azby, because a becomes z, b becomes y, etc. Under azby, "THIS IS A CIPHER." becomes GSRH RH Z XRKSCI.
We should note that this method is more effective in Hebrew, which has no vowels, than Greek, which does. A reversed Hebrew word is still a consonental text, readable as long as proper vowels are supplied. A Greek word is likely to become nonsense -- IHSOUS becomes PSQKEQ, which even if it were pronounceable, wouldn't be spelled that way. You could invoke a variation on this, in which consonants substitute for consonants and vowels for vowels. In this case, we have
|
A E H I O U W |
W U O I H E A |
b g d z q k l m n x p r s t f c y |
y c f t s r p x n m l k q z d g b |
Under this, IHSOUS becomes the odd-but-at-least-pronounceable IOQHEQ.
Even this could probably be improved -- for example, to maintain (mostly) proper inflections, one could use some sort of transposition ignoring the vowels and nu and sigma. Obviously that wouldn't do much with IHSOUS, but PETROS under the above scheme would be LEZKOS, which is pretty funny-looking, but pronounceable and inflectable.
There is no obvious evidence of such usage in the New Testament -- but who knows? Maybe you can find one. (I have a feeling I just created an excuse for a few zillion wild emendations.... Anyone have a way to reorganize the alphabet so "Thaddeus" becomes "Lebbaeus"?)
There are many more advanced forms of substitution ciphers. One method involves adding symbols for particular words (e.g. in English a symbol for "the" would be most helpful, and also for "and" and some other words). Others involve tricks such as the continuous Caesar cipher described above. Fortunately, these were largely unknown in the manuscript era, so we can pass them by. Nor will the author offer advice on the solving of substitution ciphers. The problem is that different languages involve different frequency tables and different rules. In English, for example, the most common word is "the." Technically, this is true in Greek also -- but Greek inflects the article, so particular forms (e.g. o, to) are not as common as the uninflected word kai. Each language -- indeed, each dialect -- involves its own tools for deciphering. (For a Greek example, see Tools and Examples.) The principles are the same, but the data used differs.
We should perhaps add a warning here: One must always be careful to assure that there is an actual cipher in use. Trying to "solve" something that isn't in fact encrypted can produce extreme silliness -- as the various attempts to decrypt the Apocalypse show. Another example of this is the diary of Samuel Pepys. When it first was discovered, everyone thought it was encrypted, and various people went to great lengths to "crack" his cipher. It wasn't until decades later that it was discovered that Pepys wasn't using a cipher; he was simply using Shelton's method of tachygraphy, a well-known shorthand system which also had the advantage of using less space. What the experts thought was encryption was in fact merely a method of what we would now call compression, and all that should have been needed to crack it was to open up a copy of Shelton's widely available book.
Even more hilarious is Athanasius Kircher's reconstruction of Egyptian hieroglyphs. According to Simon Singh's The Code Book, p. 204, Kircher translates the name of Pharaoh Apries as "the benefits of the divine Osiris are to be procured by means of sacred ceremonies and of the chain of the Genii, in order that the benefits of the Nile may be obtained." This was bad enough in dealing with an ancient language -- but think what such ambiguous decrypts could produce when dealing with a real cipher. A proper cipher will be unambiguous when decrypted -- that is, while you may have choices in enciphering (e.g. in a cipher which uses numbers for letters, 12, 13, 33, and 48 might all mean e, but each of those numbers means e and only e). Ambiguous readings -- except in summarization ciphers -- destroy the whole point.
So let's turn to the other major sort of ancient encryption, the transposition cipher. Unlike a substitution cipher, where one letter is replaced by another, a transposition cipher involves rearranging the order of a message. For example, one trick is to take alternate letters and place them in order. To once again use "THIS IS A CIPHER," think of placing alternate letters on alternate lines:
T I I A I H R H S S C P E
Then combine the lines to yield TIIAIHRHSSCPE. To decipher, you just cut the message in half and then reverse the above procedure. The advantage of transposition ciphers is that, though they preserve the standard frequency table of letters, the results make no sense.
Transposition ciphers, in fact, began with what appears to have been the oldest-ever encryption machine, the Spartan skutalh, a stick with the edges shaved into the shape of a prism described by Thucydides. A message written on a straight piece of parchment was wrapped around the skutalh, then copied down the columns, and transmitted; it was read by means of a skutalh with the same number of sides. Since the skutalh necessarily had more than two sides, it produced if anything a more complex transposition than the above (though it's hard to believe that others did not imitate the thing).
The key to recognizing a transposition cipher is to note that the frequency table matches that for an unencrypted message. That is, if the message is in English, it will contain very many instances of E, T, and A, and very few of Q or Z. Something similar will be true with other languages, though their frequency tables differ.
Again, modern ciphers are much more complex than the above, but they are not our concern. The currently-popular method of public key cryptography, for instance, is possible only with computers. (It relies on finding very large prime numbers.) So far as we know, all ancient ciphers were either simple substitutions or simple transpositions -- and I know of no instances of the latter in literary works, though my knowledge may well be incomplete. (There are a few ancient codes, to be sure, and not all of these have been solved, simply because our samples are so small.)
In any case, we as textual critics do not have to be concerned with the original "autographs" of the messages. If the encrypted message is intact, textual criticism does not come into play. Our concern is the case where the message has been damaged in transmission. When one has an intact message, one generally can be confident that it has been decrypted when the entire message, as decrypted, makes sense. With a corrupted original, this will not happen.
The trick in that case is to decide how much error one can accept. Let's look at the error we had above, in which we THIS IS A CIPHER was encoded with a Caesar cipher, but then erroneously transmitted as WRLV LU D FLSKHU. This decrypted as TOIS IS A CIPHER. To "correct" this to THIS IS A CIPHER means changing only one letter, and that an error relatively easy to make (K and R are readily confused in some scripts).
But now suppose you encounter a message WKLV MU D FLTKHU. Using the Caesar decrypt gives you THIS JS A CIRHER. You have two errors, both interesting -- because both could more easily occur in the plain text than in the cipher text! Was there an error in the original, or an error in the copying -- or have you not solved the cipher?
In fact, you have not solved the cipher, not quite. The above example was encrypted using a modified Caesar cipher: The bulk of the message was shifted three letters (standard Caesar), but every fifth letter (in this case, the first letter of IS and the P in CIPHER) were encrypted with a Caesar shift of four letters instead of three. In a sample this small, you can't really prove the matter. In a longer passage, such regular errors would be more obvious.
So we must somehow evolve criteria for dealing with that question, How much error can we accept while still pronouncing that we have "solved" our cipher? That is really the point of the whole exercise.
There is no simple answer for this. We can't even base our calculations on what we know of the scribe's reliability elsewhere. An encrypted text may force the scribe to be more careful, and so reduce his error rate. And it remains the editor's task to try to determine why particular errors took place. In other words, one must proceed along three lines: The actual decrypting process, a measure of goodness-of-fit for the decrypting scheme, and an examination of the textual factors which might have led to corruption.
Which leads us to another interesting point: Decrypting an unknown cipher is much like making sense of an unknown language. (The two processes, in fact, use much of the same vocabulary.) For hints on how to proceed from here, the interested reader, as well as studying texts on cryptography, might want to examine the various accounts of the deciphering of Linear B and other ancient languages.
Which brings us to another warning. Something may look like an encoded message without being one. Scribes did, at times, set out to mess with the minds of their readers. A recent example of this has been somewhat in the news (at least, I found articles about it in a science and an antiquities magazine in the same month). The item involved is the so-called "Voynich manuscript," This first appeared in 1586, when it was purchased by the Holy Roman Emperor Rudolph II, and later vanished until re-discovered by Wilfrid Voynich.
The Voynich manuscript, which gives the appearance of being written in the fifteenth or sixteenth century, is in an unknown script which nonetheless appears to be alphabetic. It is quite extensive -- 230 pages! The contents resemble no known language, and yet the sheer bulk of the manuscript, plus its interesting regularities, make it appear an actual cipher and not just a collection of gibberish.
Yet ninety years of effort have completely failed to crack the cipher. Surely, if it were a known language, it would have been decrypted by now. Yet it has not, and it is too recent for there to be any likelihood that it is based on a dead language. The suspicion is that it is a hoax (the name of the Elizabethan forger Edward Kelley has been mentioned as a possible hoaxer). Recently, Gordon Rugg has reconstructed a method, based entirely on techniques known in the sixteenth century, which could have been used to produce the manuscript. It is nearly certain, now, that the document is a forgery (though the connection with Kelley is of course unproved).
This does not tell us anything about any other ancient encrypted message, of course. But it does remind us that hoaxes did and do exist; not every seemingly-garbled message actually has meaning behind it!
If you actually want to try your hand at some Greek cryptography, we can offer examples showing the technique. We'll start with a fairly simple one. Here is the message you might receive. Two clues: It's a monoalphabetic substitution cipher, and space means space. (A major help, that.)
(The above is shown as a graphic to ensure we agree on our representations of characters. The text as it would appear using the symbol character set is HIPKWOF LD CHFIFH UFMPYEP QHFY WSPYFM HKKH QD AHAFH MDCFHXPQP QHFY IP WSPYFM QPKPFOF UFMPYEP PM QG MOLG UPUSHCQHF OQF PM PQPSOUKGYYOFY AHF PM RPFKPYFM PQPSGM KHKDYG QG KHG QOTQG AHF OTI OTQGY PFYHAOTYOMQHF LOT KPUPF ATSFOY GYQP HF UKGYYHF PFY YDLPFOM PFYFM OT QOFY CFYQPTOTYFM HKKH QOFY HCFYQOFY D IP CSOWDQPFH OT QOFY HCFYQOFY HKKH QOFY CFYQPTOTYFM.)
A solution, with explanation of how you might find it, is here. The solutions page also contains several other ciphers you can try, and some additional tools.